Dirty Frag LPE Chains Two Kernel Flaws to Root Across Major Linux Distros
TL;DR Summary
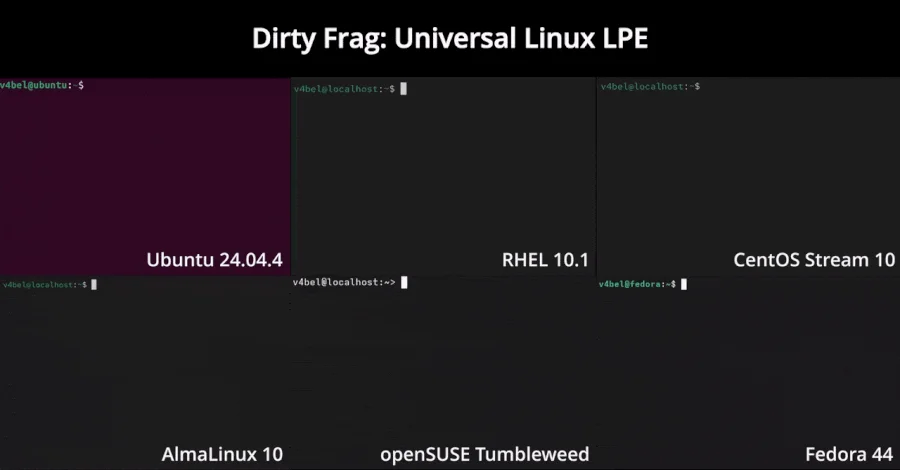
Security researchers have disclosed Dirty Frag, a new unpatched Linux kernel local privilege escalation that chains two bugs—xfrm-ESP Page-Cache Write and RxRPC Page-Cache Write—to grant root on most distributions (e.g., Ubuntu 24.04.4, RHEL 10.1, Fedora 44). There is no CVE yet, and a working PoC exists; exploits are being weaponized in the wild. Patches are not yet available, so admins are advised to block esp4, esp6, and rxrpc modules until fixes arrive. The flaw sits in in-place decryption paths for paged fragments in esp4/esp6/rxrpc, allowing plaintext access and privilege escalation even if other mitigations like algif_aead are in use.
- Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions The Hacker News
- CVE-2026-31431: Copy Fail vulnerability enables Linux root privilege escalation across cloud environments Microsoft
- CISA Warning: High-Severity Linux Flaw Puts Unpatched Systems at Risk TechRepublic
- ‘Copy Fail’ is a real Linux security crisis wrapped in AI slop CyberScoop
- How Cloudflare responded to the “Copy Fail” Linux vulnerability The Cloudflare Blog
Reading Insights
Total Reads
0
Unique Readers
2
Time Saved
3 min
vs 4 min read
Condensed
86%
694 → 99 words
Want the full story? Read the original article
Read on The Hacker News