
Cybersecurity News
The latest cybersecurity stories, summarized by AI
Featured Cybersecurity Stories


Defender for Endpoint Tests Auto-Isolation to Stop Lateral Movement
Microsoft Defender for Endpoint is previewing automatic isolation as part of Automatic Attack Disruption, automatically isolating suspected-compromised onboarded endpoints to limit attacker lateral movement and data exfiltration while keeping the device monitored; security operators can release the device after investigation, with the feature expanding prior isolation capabilities across Windows and Linux devices and user accounts.

More Top Stories
Massive Laravel-Lang Breach Sparks Cross-Platform Credential Theft
The Hacker News•11 days ago
AI Flags 10,000+ Critical Flaws, Accelerating Patch Push Worldwide
The Hacker News•11 days ago
More Cybersecurity Stories

Global raid shuts down ransomware-linked VPN First VPN and seizes its infrastructure
An international operation led by France and the Netherlands, with Europol/Eurojust support, dismantled the ‘First VPN’ service used by ransomware and data-theft actors. Authorities seized 33 servers across 27 countries, shut down key domains, disrupted infrastructure, and arrested the administrator in Ukraine. Investigators infiltrated the VPN to recover data, with Europol reporting 506 identified users and 83 intelligence packages shared to aid ongoing investigations into ransomware and related crimes. While VPNs have legitimate uses, criminals leveraged this service to hide activity; all identified users have been notified and further legal action may follow.
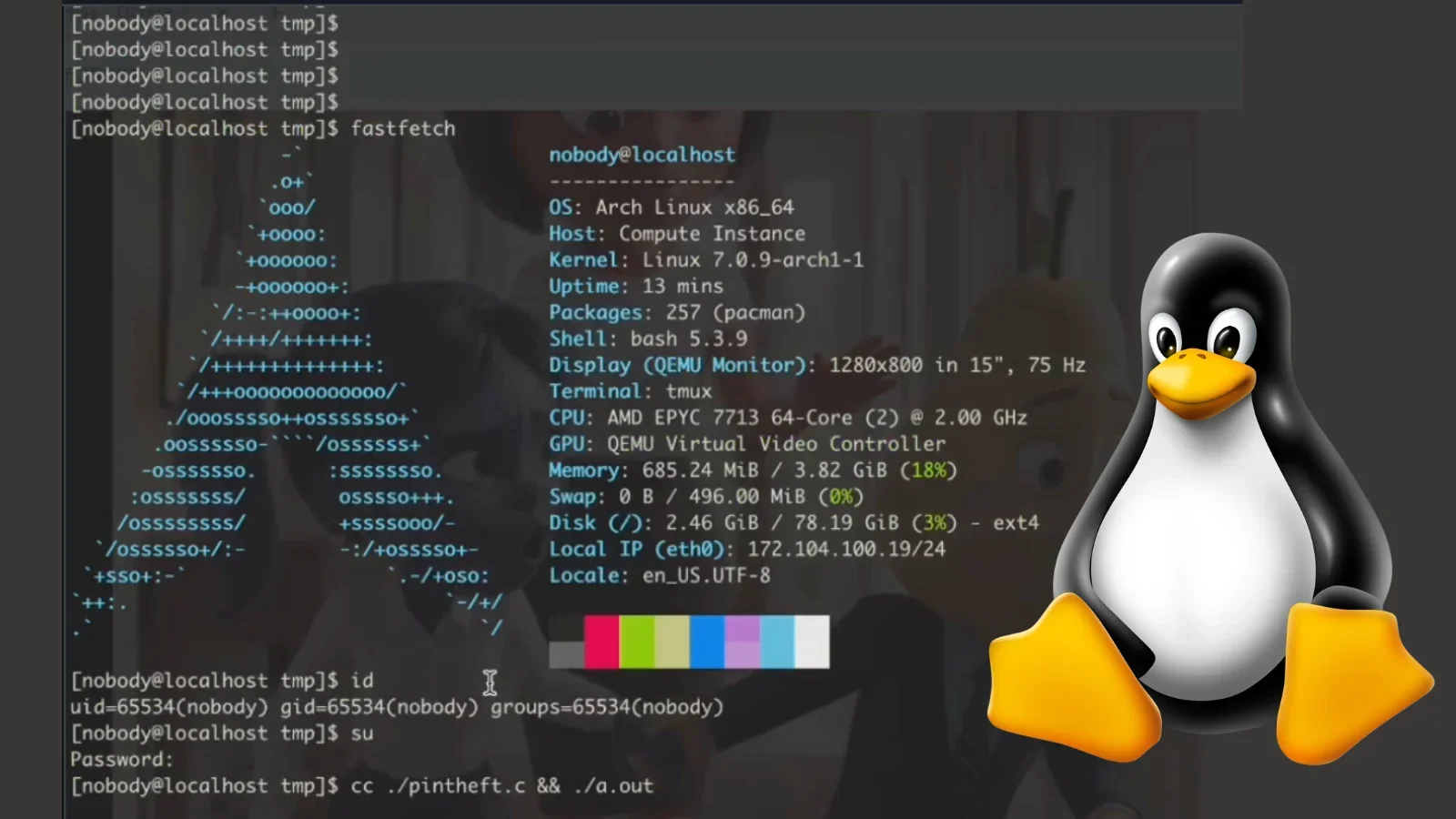
PoC Unleashes PinTheft Linux LPE, Unlocks Root Access
A proof-of-concept exploit named PinTheft has been published for a Linux kernel local privilege escalation, leveraging an RDS zerocopy double-free flaw to gain root access under specific kernel configurations. The PoC demonstrates a novel way to steal references via io_uring and overwrite in-memory pages, underscoring ongoing Linux kernel security challenges. Admins should apply latest patches or blacklist vulnerable modules to mitigate risk.

Millions at Risk as NGINX Zero-Day RCE Flaw Sees Real-World Exploitation
Security researchers say CVE-2026-42945, a heap buffer overflow in NGINX Open Source and NGINX Plus, is being actively exploited in the wild. The flaw can crash NGINX worker processes via crafted requests, with remote code execution possible only if ASLR is disabled and a specific rewrite configuration is present; despite ASLR generally enabled, estimates show up to 5.7 million internet-facing servers may be affected. Organizations should patch promptly, ensure ASLR remains enabled, and audit rewrite rules to mitigate risk while threat actors rapidly scan for vulnerable systems.
Week in Security: Exchange Zero-Day Exploited, NPM Worm Surges, and AI Supply-Chain Risks
This weekly security roundup highlights rapid, multi-vector threats: on-prem Microsoft Exchange is being exploited via CVE-2026-42897 (spoofing/XSS), Cisco’s SD-WAN Controller faces active exploitation from CVE-2026-20182, and a TeamPCP‑driven wave poisons TanStack npm packages as part of a larger supply-chain campaign. The era of fake AI repos delivering stealer malware continues (Open-OSS/privacy-filter on Hugging Face). AI-assisted vulnerability discovery is accelerating with OpenAI’s Daybreak and Microsoft MDASH, alongside other notable findings (ransomware deals, new CVEs, and cross‑platform E2EE deployments). The takeaway: patch early, rotate keys, and assume software supply chains are compromised.

Admin Access Wipeout: Burst Statistics Plugin Flaw Exposes WordPress to Takeover
A critical vulnerability in the Burst Statistics WordPress plugin (versions 3.4.0–3.4.1.1, CVE-2026-8181) allows unauthenticated attackers to bypass authentication and impersonate an administrator via crafted REST API requests, potentially creating a new admin account and taking over a site. Discovered May 8, 2026 by Wordfence’s PRISM, it was patched in version 3.4.2 on May 12, 2026. The flaw stems from improper handling of authentication in the MainWP integration, enabling exploitation across REST endpoints. admins should immediate patch to 3.4.2+, audit user accounts, and monitor logs to prevent compromise.

Confidently Wrong: AI Hallucinations Threaten Cybersecurity
AI hallucinations are confidently plausible yet factually incorrect outputs that can mislead security decisions, causing missed threats, false positives, and risky remediation. A 2025 AA-Omniscience benchmark found most models favor confident, incorrect answers over correct ones on hard questions. Mitigation includes enforcing human review before actions, auditing training data as a security asset, enforcing least-privilege access, investing in prompt engineering, and centering identity security in AI governance.

AI-Driven Zero-Day Discovery Linked to 2FA Target, Google Says
Google’s Threat Intelligence Group says a prominent cybercrime group used an AI-assisted zero-day in a Python script to target a popular open-source web-based system administration tool, potentially bypassing two-factor authentication; Google and the vendor coordinated a disclosure and patch, noting Gemini was not involved and that the attackers likely leveraged AI to discover and weaponize the flaw, amid broader debates around Mythos hype.

AI-Designed Zero-Day Bypasses 2FA in Mass Exploitation Campaign
Google Threat Intelligence Group revealed a zero-day exploit—likely AI-assisted—that enables bypassing 2FA on a popular open-source admin tool and was used in a mass exploitation campaign; the Python-based exploit shows patterns typical of LLM-generated code, and Google coordinated with the vendor to patch the flaw and disrupt the operation, while the report also highlights broader AI-enabled threats including autonomous malware and AI-assisted misuse of Gemini.

MuddyWater Uses Teams to Harvest Credentials and Subvert MFA in Chaos False-Flag Campaign
Security researchers describe a MuddyWater operation that exploited Microsoft Teams for external contact and screen-sharing to harvest user credentials (credentials.txt/cred.txt) and push MFA changes, followed by backdoor access using DWAgent and AnyDesk. The attackers deployed a custom RAT (Game.exe) and used C2 domains linked to MuddyWater, framing the intrusion as a Chaos ransomware false-flag campaign focused on credential theft and data exfiltration rather than encryption. The campaign featured indicators like a forged code-signing certificate and stolen credentials enabling lateral movement to Domain Controllers.

Extortion group claims 280 million education records stolen in Canvas breach
A hacker group called ShinyHunters claims it stole 280 million student and staff records from 8,809 schools, districts, and online education platforms through a breach of Instructure's Canvas, exposing names, email addresses, and private messages; the alleged list of affected institutions hasn’t been independently verified, universities are assessing potential impact, and Instructure hasn’t publicly responded.
