Two Actively Exploited Defender Flaws Prompt Auto-Patch Rollout
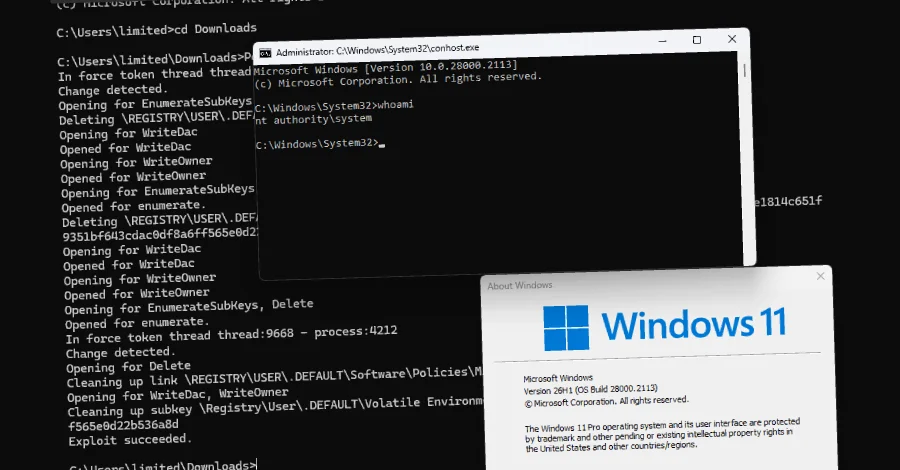
Microsoft warns that Defender is under active exploitation due to a privilege-escalation flaw (CVE-2026-41091) and a separate denial-of-service flaw (CVE-2026-45498). Updates are delivered automatically via Defender Antimalware Platform versions 1.1.26040.8 and 4.18.26040.7, and systems with Defender disabled are not affected. CISA has added both flaws to its Known Exploited Vulnerabilities catalog, with a June 3, 2026 patch deadline for Federal Civilian Executive Branch agencies. The article also references older Microsoft CVEs that have been added to KEV in recent weeks.