TA446 Expands DarkSword iOS Attacks in Broad Spear-Phishing Campaign
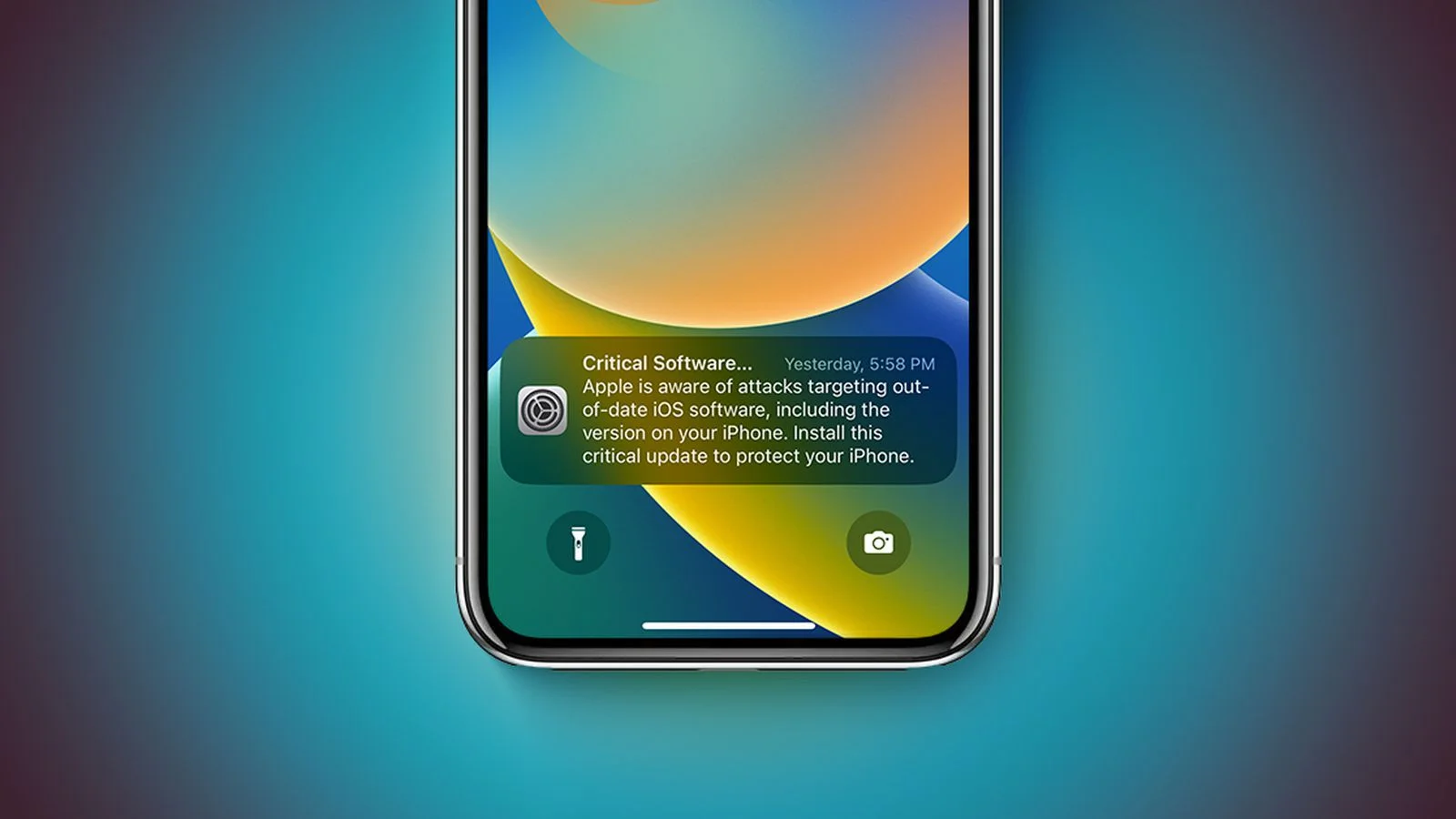
TA446, a Russia-linked threat group, used the DarkSword iOS exploit kit in a targeted spear-phishing operation to deliver the GHOSTBLADE dataminer and the MAYBEROBOT backdoor via password-protected ZIPs; emails spoofed Atlantic Council discussion invites and redirected iPhone users (March 26, 2026) to the exploit kit through decoy PDFs, with server-side filtering guiding iOS browsers to the kit but no sandbox escapes observed. The campaign broadened targets to government, think tanks, higher education, finance, and legal entities, suggesting opportunistic credential harvesting and intel collection. Apple warns users with Lock Screen alerts and urges updates; a leaked DarkSword version on GitHub could democratize the exploit, potentially expanding mobile threats, per researchers.