ConsentFix v3 automates OAuth abuse to hijack Azure accounts
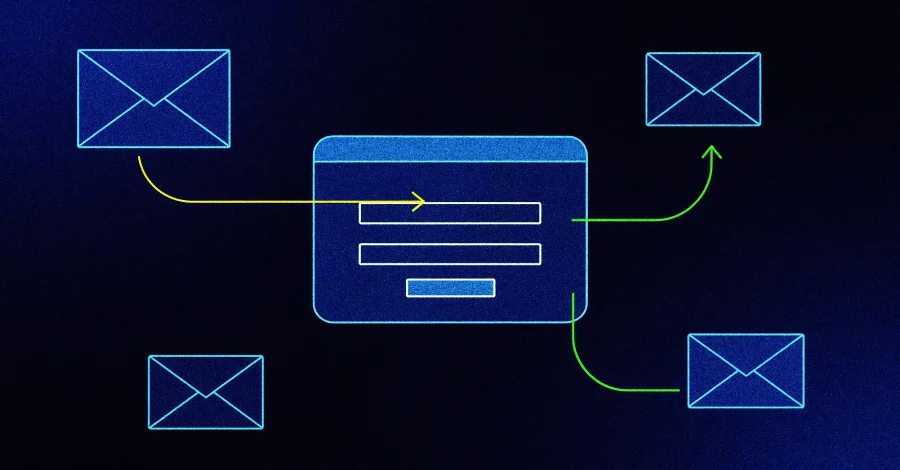
Security researchers describe ConsentFix v3, an automated phishing workflow that exploits the OAuth2 authorization code flow to steal tokens and hijack Microsoft/Azure accounts. The campaign uses Pipedream as the automation engine, hosts a spoofed Microsoft login on Cloudflare Pages, and exfiltrates the OAuth code to immediately exchange it for tokens, enabling access to emails and files even with MFA. Mitigations include token binding, behavioral detection rules, and app authentication restrictions; it remains unclear how widely this variant is being adopted.