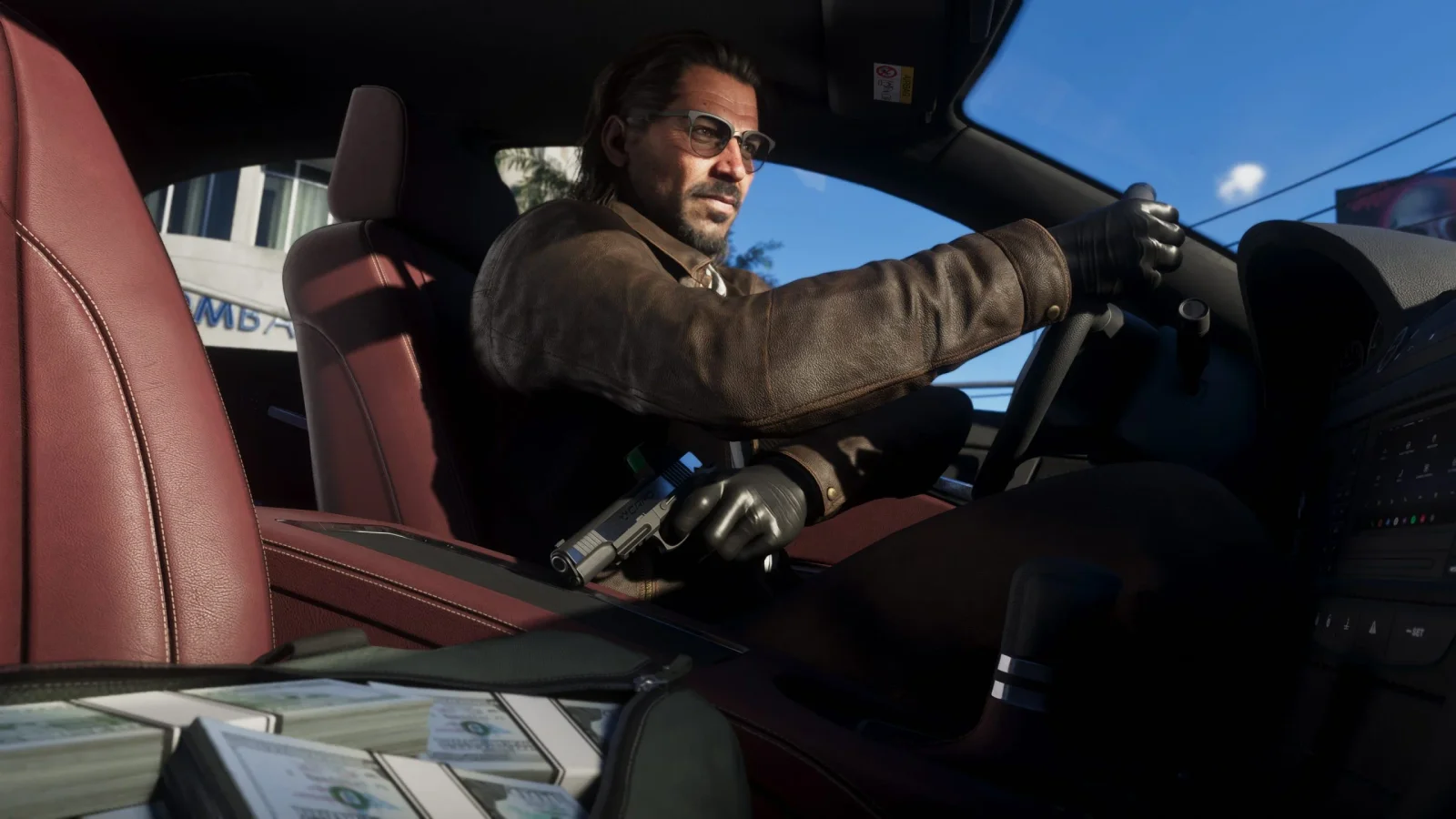
GTA 6 Pre-Order Buzz Triggers Malware Warnings
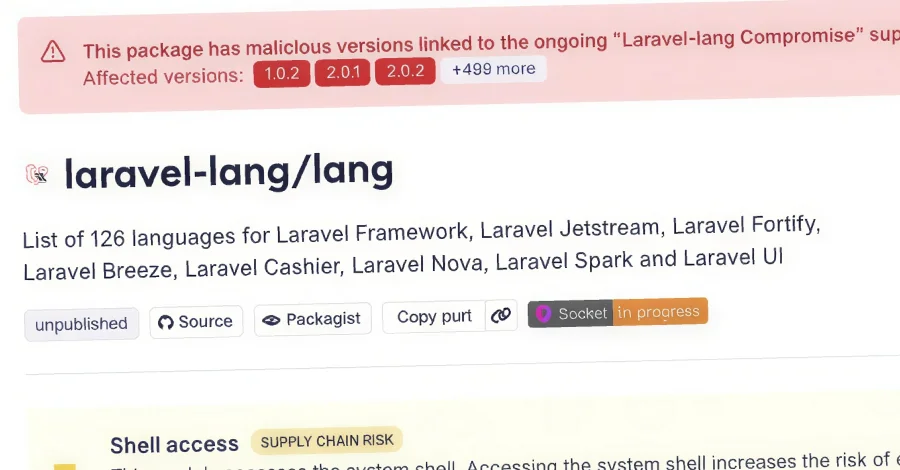
GTA 6’s release hype has outpaced official pre-orders, leading to a wave of scams that promise free codes, beta keys, or exclusive trailers and deliver malware via fake installers and phishing sites. NordVPN Threat Intelligence found clone sites and trojan Android adware targeting fans, emphasizing that only official channels should be trusted for GTA 6 information and access.