TrapDoor Strikes npm, PyPI, and Crates.io with Cross-Ecosystem Credential-Stealing Malware
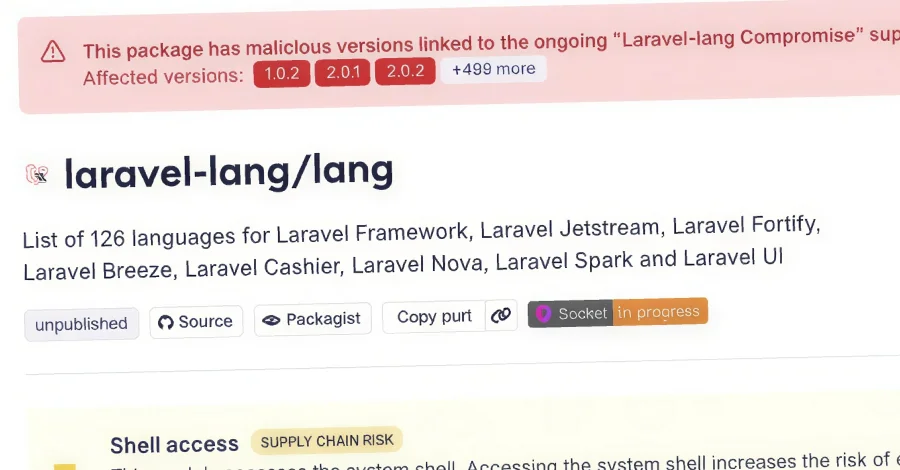
A coordinated TrapDoor campaign targets npm, PyPI, and Crates.io, distributing 34 malicious packages across hundreds of versions to steal developer secrets, crypto wallets, SSH keys, cloud credentials, and environment data. npm payloads run trap-core.js to harvest credentials and establish persistence via cron, systemd, Git hooks, and SSH lateral movement; Rust crates search keystores and exfiltrate data to GitHub Gists; Python packages auto-execute on import and fetch a remote JavaScript payload executed via node -e. The attack also hides instructions in .cursorrules and CLAUDE.md to trick AI tools through PRs, signaling an evolution of developer-workflow attacks across multiple ecosystems.