Chrome Extensions to Elevate Your YouTube Experience
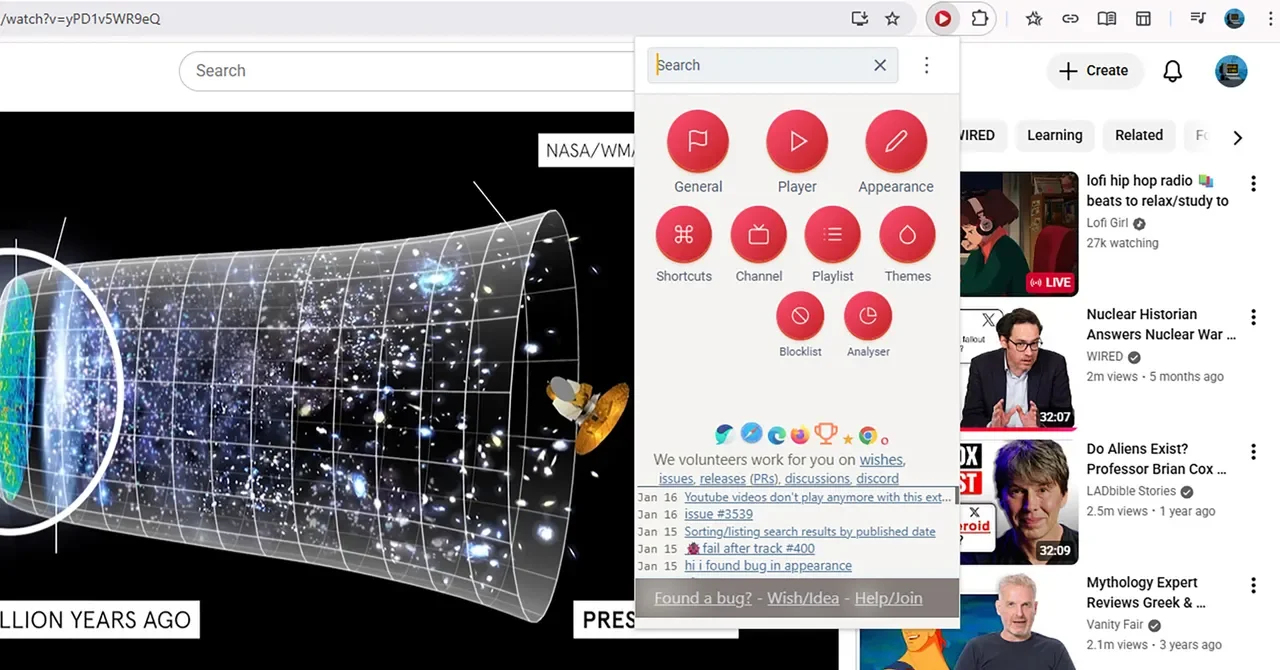
WIRED highlights five Chromium-based extensions—Improve YouTube, Enhancer for YouTube, PocketTube, Turn Off the Lights, and DeArrow—that enhance YouTube with UI tweaks, playback controls, subscription organization, screen dimming to reduce distractions, and crowdsourced improvements to video titles and thumbnails, all without focusing on ad blockers.