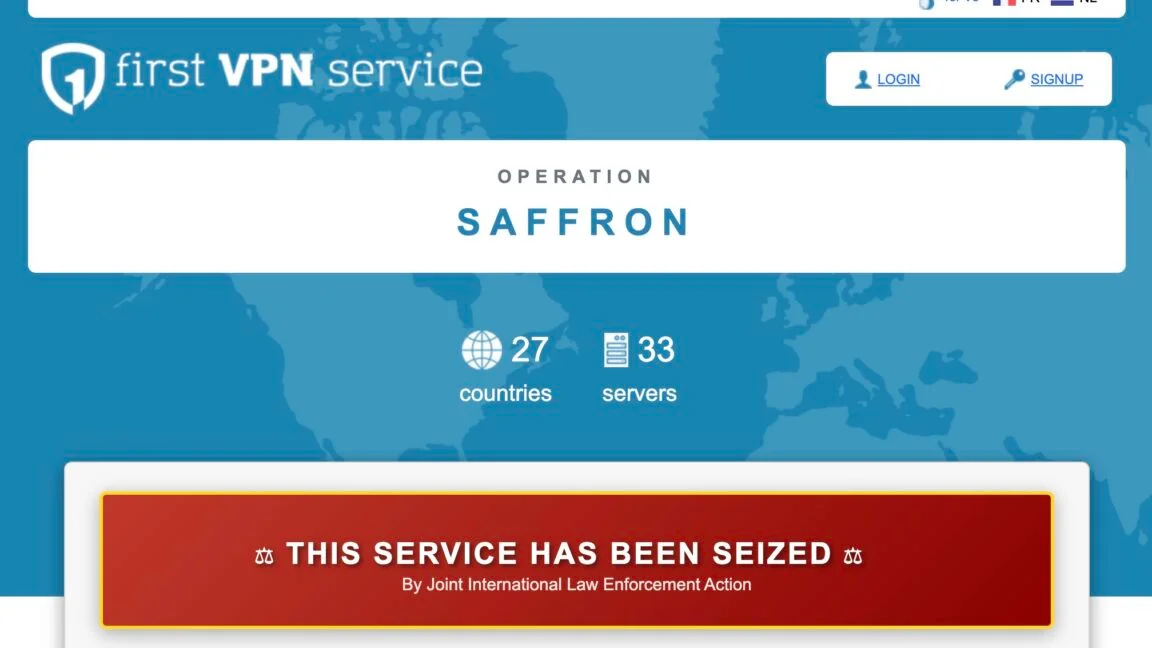
European Police Dismantles First VPN, Unmasks Thousands of Criminals
European authorities led by France and the Netherlands, with Europol and Eurojust, dismantled the First VPN service used by cybercriminals for ransomware and data theft. Investigators infiltrated the service, seized 33 servers, and arrested its administrator, identifying about 506 users and producing 83 intelligence packages that supported 21 Europol-facilitated investigations. The operation underscored how VPNs marketed as ‘no-logs’ can mislead users who believe they are safe, even as criminal activity relies on such infrastructure.