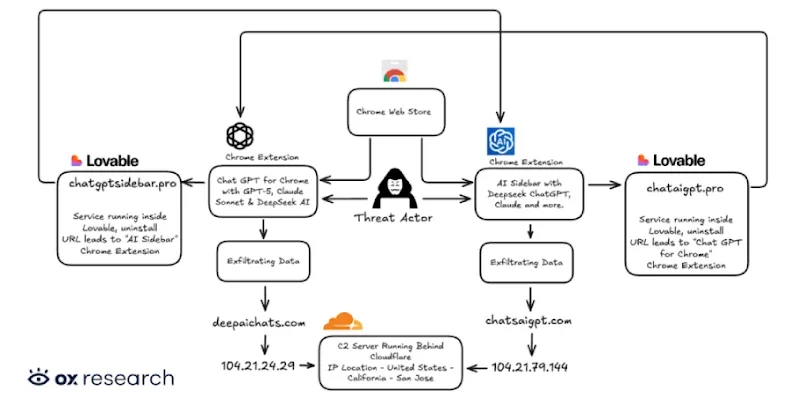
GitHub breach tied to poisoned VS Code extension hits thousands of internal repos
GitHub confirmed that a poisoned Visual Studio Code extension installed on an employee’s device led to the exfiltration of roughly 3,800 internal repositories; the malicious extension was removed from the VS Code Marketplace and the endpoint isolated, with incident response begun. Current assessment indicates only GitHub’s internal repositories were affected and there is no evidence that customer data outside the affected repos was compromised. The TeamPCP group has claimed access to about 4,000 repos on a cybercrime forum, though attribution remains unsettled. This follows a history of trojanized VS Code extensions used to steal code and credentials.