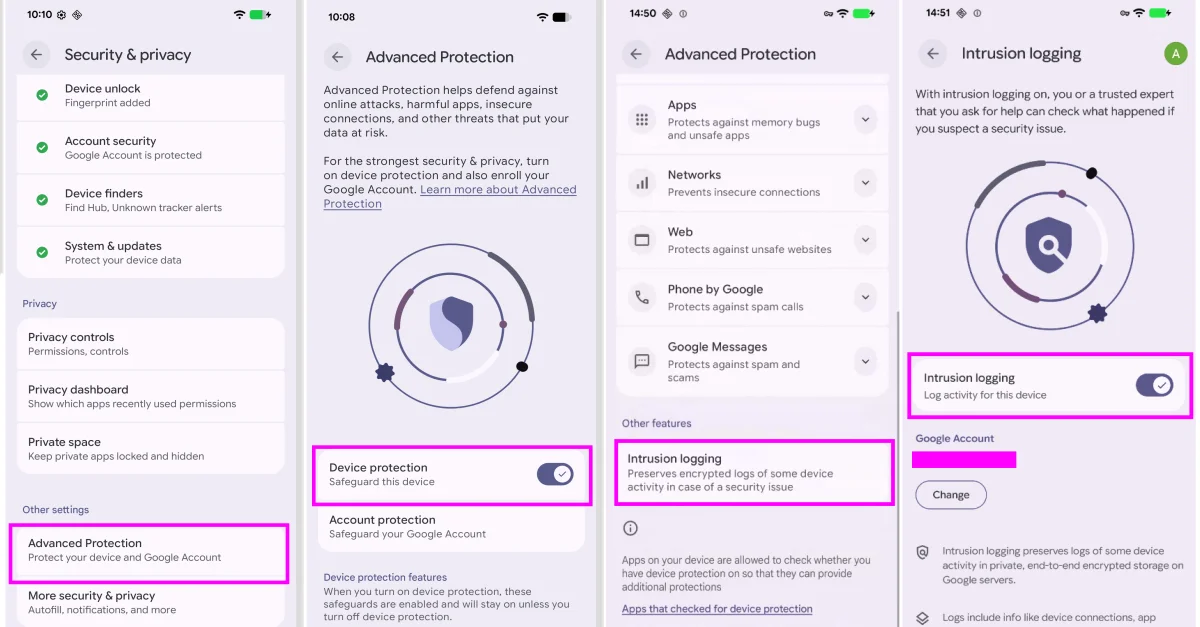
Android Debuts Forensic Intrusion Logs to Aid Spyware Investigations
Google is rolling out opt-in Intrusion Logging in Android's Advanced Protection Mode to store end-to-end encrypted forensic logs for investigating sophisticated spyware; developed with Amnesty International and Reporters Without Borders, the logs capture daily device and network activity, are retained for 12 months and can be downloaded by users (including Chrome Incognito activity), with encryption keys protected by the user's Google account password and device credentials.